Crafting exceptional software solutions exclusively designed for your business needs. Learn More

Most businesses ask the security question at the wrong point. They evaluate a no-code platform's features first, pick a template, start building workflows, and then ask the IT team to check if it is secure. Well, the architecture of data security in no-code platforms does not work that way.
In a no-code platform, the security is built into the stack before a single user logs in, and understanding that layered structure is what separates businesses that implement a solution confidently from those that hesitate indefinitely.
In this blog, we will explore every potential point to understand how a no-code platform handles security and access control.
Why Security Should Be Built Into the Stack?
No-code platform security features operate across multiple layers, working simultaneously to protect the system. And the platform handles server hardening, network firewalls, and protection against distributed attacks at the infrastructure level.
If we move up the stack, at the application layer, it manages authentication, session integrity, and input validation. Similarly, at the data layer, it enforces encryption and access rules. Importantly, each of these layers is maintained by the platform vendor rather than your internal team.
However, this multi-layered structure is truly tested through multi-tenancy isolation. In such environments, hundreds of companies can share the same underlying infrastructure, yet each company’s data remains completely invisible to others. To understand this better, here is how that separation works.
- Unique tenant identifiers are assigned to every dataset. As a result, no query, export, or API call from one company can access another company’s records, regardless of how the underlying servers are structured.
- Metadata-layer enforcement plays a critical role in maintaining security. It allows the platform to manage the rules governing your business logic without exposing the raw database to end users. Specifically, it tracks data about data, including your tables, relationships, and permissions, as a separate and protected layer.
As a result, your application’s structure remains visible to the right people within your organization, while the underlying database stays completely inaccessible to anyone outside the defined permission boundaries.
Three Layers of Encryption That Protect Your Data End to End
Every byte that moves between a user's browser and the platform travels inside a TLS 1.3-encrypted tunnel. This ensures that data in transit remains secure at all times.
In addition to this, no-code platforms use AES-256 encryption for data stored within the system. Therefore, even if someone gains physical access to the server hardware, the data remains unreadable without the decryption key.
Beyond these two layers, field-level security introduces a third layer that is often overlooked. But it is equally important. To better understand its role, here is what that looks like:
- Data in transit is wrapped inside a TLS 1.3 tunnel the moment it leaves a user's browser. As a result, it becomes unreadable to anyone attempting to intercept the connection mid-route.
- Data at rest is stored using AES-256 encryption, which is the same standard used across government and financial infrastructure. Therefore, even hardware-level access does not expose any usable information without the required keys.
- Field-level encryption allows specific sensitive fields, such as a salary figure, a national ID number, or a credit card reference, to carry their own separate encryption key. This key remains distinct from the rest of the record.
Finally, this last point is particularly important for businesses operating in healthcare, finance, or legal sectors. In such cases, a breach at the record level does not automatically expose every sensitive field within it. Additionally, the way field-level rules interact with structured data is explored further in our guide on no-code databases.
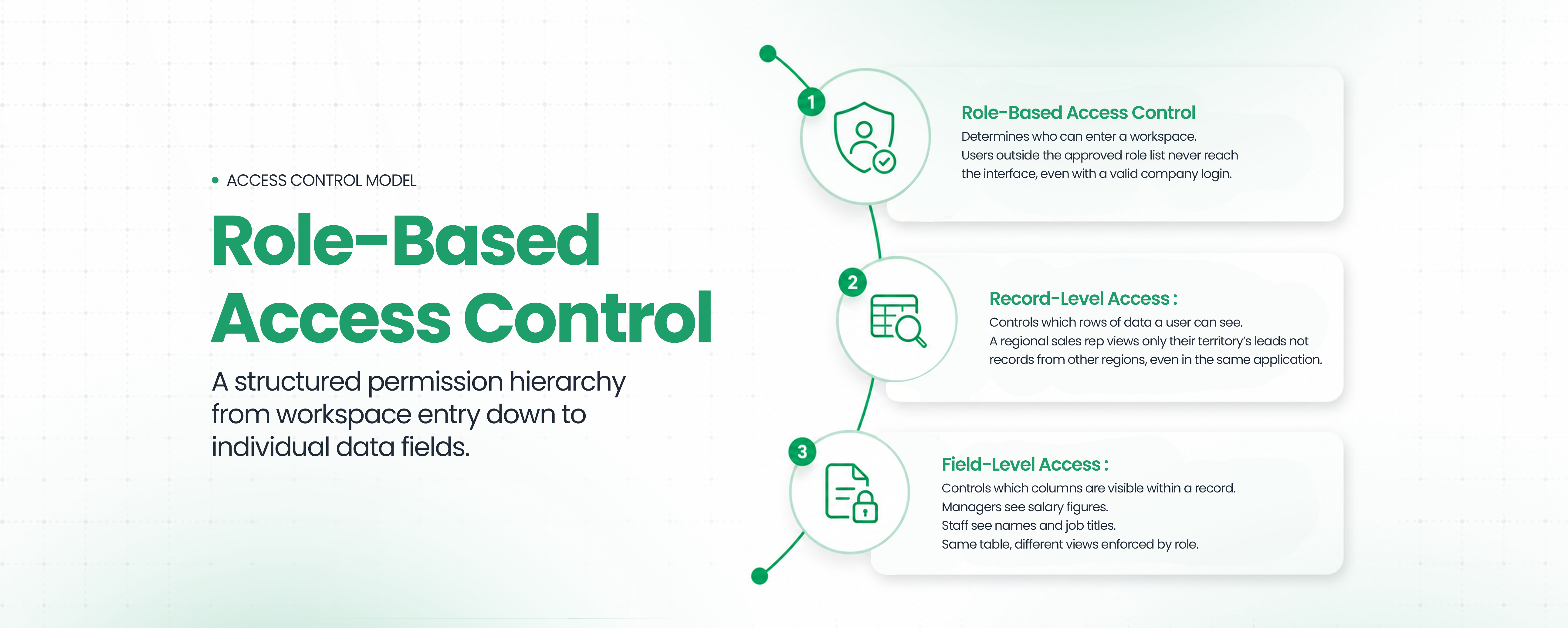
How Role-Based Access Control Works Inside a No-Code App

Role-based access control is a core component of data security in no-code platforms, as it determines who can access, view, and interact with data at every level of an application. In enterprise no-code security, this is not a simple on or off permission. Instead, it is a structured system designed to prevent unnecessary data exposure while ensuring users can perform their roles effectively.
Within no-code development platforms, role-based access control operates across a hierarchy of permission levels, with each level becoming more granular than the last. This layered approach ensures that access control in no-code platforms is enforced consistently across users, teams, and workflows.
To understand how this works in practice, let us look at each level more closely:
- App-level access controls who can enter a workspace at all. As a result, users outside the approved role list never reach the interface, even if they have a valid company login. This acts as the first layer of protection within no-code platform security features.
- Record-level access controls, which rows of data a user can see. For example, a regional sales representative can view only their assigned territory’s leads and nothing from other regions, even though they are using the same application. This prevents unnecessary exposure of business-critical data.
- Field-level access controls determine which columns are visible within a record. For instance, a manager can see salary figures, while staff members can only view names and job titles. This ensures that sensitive data remains restricted even within shared datasets.
Together, these layers form a practical implementation of access control in no-code platforms, where data visibility is tightly aligned with user roles and responsibilities.
In addition to these controls, CodeBlox integrates role-based access control with identity providers such as Azure AD, Okta, and Google Workspace through Single Sign-On. This ensures that user permissions remain synchronized with organizational roles. When someone joins, changes roles, or leaves the organization, their access is updated automatically through the connected directory.
Furthermore, the 2026 IBM RBAC Implementation Guide highlights that structuring access around least-privilege principles significantly reduces the overall attack surface within an organization. This is the same principle applied across CodeBlox, where access control is designed to support enterprise no-code security without requiring manual intervention.

The Three-Layer System That Keeps Your APIs Secure
API security in no-code platforms does not rely on a single mechanism. The three controls work together to ensure authentication, prevent overload, and maintain accountability for every external request made to the platform.
To better understand this, let us look at how each control functions in practice:
- OAuth 2.0 and API key authentication require every external request to present a verified credential before the platform responds. As a result, requests without a valid token or key receive no response, regardless of their origin.
- Rate limiting and throttling cap the number of requests a single user or integration can make within a defined time window. This not only prevents accidental overloads caused by misconfigured automations but also protects against deliberate abuse from bots targeting the application.
- Audit trails log every API call with a timestamp, the requesting identity, the endpoint accessed, and the response code. Consequently, this creates a permanent record that security teams can review at any point.
In addition to these controls, industry insights further reinforce the importance of structured API security. The 2025 Global State of API Security report identifies broken object-level authorization as one of the most commonly exploited API vulnerabilities across industries.
However, in no-code platforms, this risk is addressed at a structural level. Since users interact through abstracted interfaces rather than writing raw queries, the platform’s query layer automatically enforces object-level permission checks on every request.
No-Code vs. Traditional Development on Security
The operational difference between the two approaches becomes clearest when you look at day-to-day security maintenance rather than the initial setup. In practice, the contrast is not just technical but also operational, as it directly impacts how consistently and efficiently teams can manage risk over time.
Platforms like CodeBlox are designed to eliminate fragmented security ownership by centralizing critical security functions at the platform level. Instead of treating security as an application-specific responsibility, CodeBlox standardizes and automates it across every application built on the platform.
As the table illustrates, traditional development requires teams to handle each security responsibility independently. In contrast, no-code platforms standardize and centralize these processes.
For instance, in custom development, each application carries its own security maintenance burden. A patch involves identifying the vulnerability, writing a fix, testing it, and then deploying it separately for each application.
On the other hand, within a no-code platform, this entire cycle is managed by the vendor. As a result, the fix is implemented once at the platform level, and every application benefits from it simultaneously, without requiring any action from your team.
How No-Code Platforms Keep Your Compliance Audit-Ready
No-code platforms like CodeBlox are designed to simplify compliance by embedding audit-readiness directly into the system. Instead of requiring teams to build tracking mechanisms from scratch, the platform ensures that every critical action is recorded automatically.
For example, every create, read, update, and delete action inside a CodeBlox application generates an immutable log entry. As a result, these automated audit logs provide compliance teams with a complete, timestamped record of who accessed what data and when. This level of traceability is a baseline requirement for certifications such as SOC 2 Type II and ISO 27001.
Furthermore, for businesses operating in regulated industries, the platform’s existing certifications serve as a strong starting foundation rather than a blank slate. In practical terms, a healthcare company does not need to build audit-ready logging from the ground up, as much of the required structure is already in place.
In addition to this, industry research continues to validate this shift. A 2025 paper in IEEE Xplore proposes standardized governance frameworks specifically for no-code security, highlighting that the sector has matured enough to establish its own formal compliance standards alongside traditional software development.



The Next Step: AI That Monitors and Adjusts Access Automatically
The current generation of access control in no-code platforms is primarily rule-based. You define permissions, and the platform enforces them. That model is now evolving toward something more dynamic and responsive, and this shift is already visible in 2026 platforms.
Instead of relying only on predefined rules, modern systems are beginning to observe user behavior and respond in real time. This introduces a new layer of security that adapts as activity patterns change.
- Behavioral analytics uses AI to analyze login patterns and flag anomalies as they happen. For example, a user authenticating from two geographic locations within minutes, or an account exporting an unusually large dataset outside normal working hours, is immediately identified as suspicious.
- Self-healing permissions take this a step further by restricting or revoking access automatically when such behavior is detected. This allows potential threats to be contained before any manual intervention is required.
The JRD Systems 2026 enterprise development report describes AI co-creation and native data capabilities as foundational to automated threat detection. This signals a clear shift from static permissions to systems that continuously monitor and respond on their own.
What CodeBlox Manages So You Can Focus on Building
Every security layer discussed in this blog, including multi-tenancy isolation, field-level encryption, RBAC, SSO integration, API authentication, immutable audit logs, and behavioral threat detection, operates beneath every application built on CodeBlox.
Your team configures access rules through a visual interface, while the underlying infrastructure requires no custom code to maintain, patch, or audit. This significantly reduces the operational burden on internal teams.
No-code does not mean security is compromised. It means the complexity of security is handled at the platform level by specialists, allowing your team to focus entirely on building workflows that drive business value. The no-code platforms guide goes into more detail about how no-code platforms facilitate scalable operations.
If you're planning to build secure, scalable applications without managing security complexity manually, this is where CodeBlox makes a difference.
{CTA button:Book a Demo with CodeBlox:https://www.codeblox.com/schedule-demo}
Frequently Asked Questions
Find answers to the most common questions about our no-code platform and how it can help you build powerful business application solutions without writing a single line of code.
What are the primary risks of using no-code platforms?
While no-code platforms provide robust safety, risks often stem from misconfigured access control in no-code platforms or "shadow IT" deployments. To mitigate these, enterprises should prioritize platforms with SOC 2 compliance and detailed audit trails, ensuring that even as development scales, enterprise no-code security standards remain consistent across the organization.
How do no-code platforms handle user authentication?
Authentication in no-code development platforms is managed through audited, pre-configured modules that support OAuth 2.0 and SAML. By leveraging these native no-code platform security features, businesses avoid the risks of custom-coded login systems. The platform provider manages patches and security updates, ensuring your authentication layer is always protected against modern threats.
Can no-code platforms integrate with existing enterprise security systems?
Yes. Enterprise no-code security relies on seamless integration with existing Identity Providers (IdPs). Platforms like CodeBlox support API security in no-code platforms by connecting via SSO to tools like Azure AD and Okta. This allows organizations to extend their corporate security policies and role-based access control directly into their custom-built apps.
How is data encrypted in no-code platforms?
Modern no-code platforms protect information using military-grade standards. Data moving between the user and the server is encrypted via TLS 1.3, while stored information utilizes AES-256 encryption. For enterprise no-code security, sensitive fields can be isolated with unique encryption keys, preventing a single point of failure from exposing the entire database.
What is role-based access control (RBAC) in no-code tools?
Role-based access control (RBAC) is a security framework that restricts system access to authorized users based on their specific job responsibilities. In no-code development platforms, RBAC provides granular access control in no-code platforms at the application, record, and field levels, ensuring that employees only interact with the data necessary for their specific tasks.